Better play it safe. I fired up my Virtual Machine and proceeded to the site. Pop-ups blocked by Firefox but either wise nothing suspicious happening.


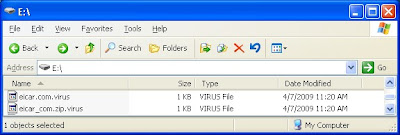
How about I try allowing the pop-ups? Lo and behold!!! A strange file mysteriously appears in my root directory. Submitted this executable file to VirusTotal and it was discovered to be a Trojan. Scary isn't it? Only 9 out of the 40 hosted AV engines detected it as malware. My hypothesis is that the hacker injected the banner ads into the website. The ads point to another site that drops the Trojan onto the victim's machine.


I ran through the same sequence again... this time on another machine with Antivir AV engine installed and updated. Antivir was able to block the malware from being injected using its heuristic scanner. Powerful!!! The Trojan's filename is randomly generated btw because the filename keeps changing when I repeat the injection multiple times.
I've contacted my toy supplier but he is unwilling to take down the site and doesn't know how to rectify the problem. I've offered my security consulting service in exchange for toys but was turned down. Out of goodwill, I offered a few remediation options but he rejected them.
Morale of the story? Be wary when surfing the dangerous web... you never know which site hosts malicious content no matter how innocent it looks.